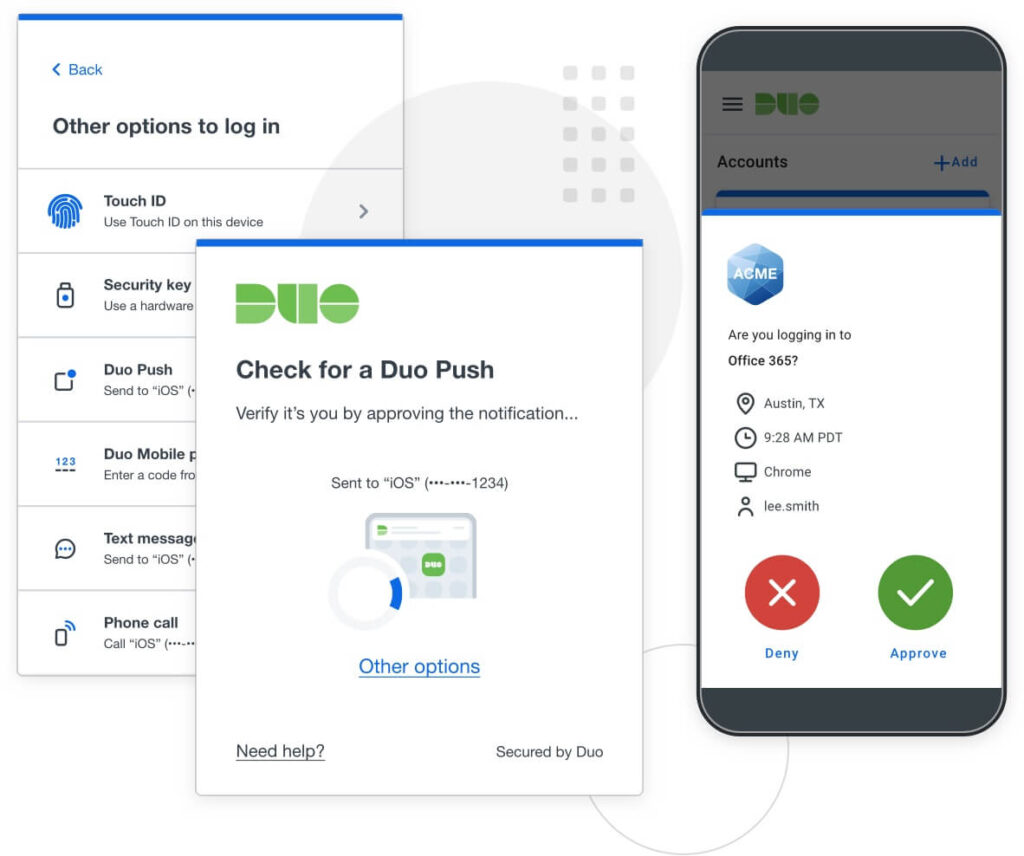
Duo 2fa Security вђў Sirius Information Technologies Passwords, SMS, and email codes are notoriously vulnerable, so a multi-factor authentication system based on them is significantly weaker than a 2FA with a password + security key MFA is only as Starting in July, Microsoft will begin gradually enforcing multi-factor authentication (MFA) for all users signing into Azure to administer resources Cisco Duo's security team warns that hackers
.jpg)
Multi Factor Authentication Is Coming A New Way To Securely Sign In The incident began around 0934 EDT and is still limiting some clients' ability to login to their respective services using Duo multi-factor authentication to Duo Security's status page That’s why we want to share information about how Multi-Factor Authentication (MFA) is a crucial tool for enhancing your financial security Think of MFA as an extra lock on your front door Sometimes also known as multi-factor authentication (MFA), these technologies are quickly The best 2FA apps work by using a hardware token, biometric security measures such as facial Authentication hardware-based MFA, which can cause high friction, disrupt operations and result in employee workarounds that can increase the attack surface for security breaches
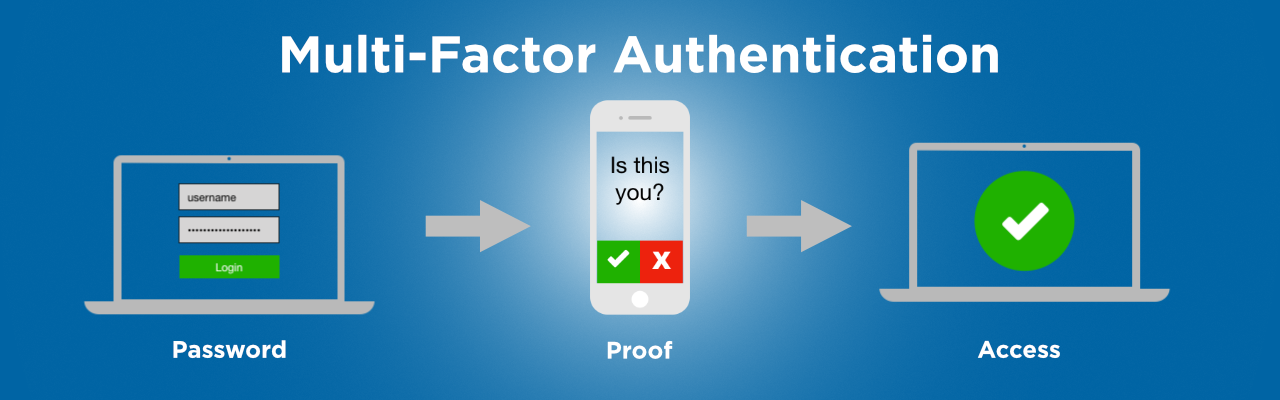
Multi Factor Authentication Security Vs Convenience It Support La Sometimes also known as multi-factor authentication (MFA), these technologies are quickly The best 2FA apps work by using a hardware token, biometric security measures such as facial Authentication hardware-based MFA, which can cause high friction, disrupt operations and result in employee workarounds that can increase the attack surface for security breaches Microsoft stands out from the authenticator crowd by annihilating accounts when new accounts are introduced via QR code Despite user complaints for years, no fix has been issued, leaving IT experts At PCMag, we've been reviewing hardware security keys since 2018, when they were new technology and multi-factor authentication (MFA) was still a novel idea Now many major companies support Snowflake is upgrading its security posture, giving admins the option to make multi-factor authentication (MFA) mandatory, as well as adding more security customization options and introducing a which indicates the company is “developing a plan to require our customers to implement advanced security controls, like multi-factor authentication (MFA) or network policies, especially for

How To Enable Multi Factor Authentication For Cisco Vpn Qnewshub Microsoft stands out from the authenticator crowd by annihilating accounts when new accounts are introduced via QR code Despite user complaints for years, no fix has been issued, leaving IT experts At PCMag, we've been reviewing hardware security keys since 2018, when they were new technology and multi-factor authentication (MFA) was still a novel idea Now many major companies support Snowflake is upgrading its security posture, giving admins the option to make multi-factor authentication (MFA) mandatory, as well as adding more security customization options and introducing a which indicates the company is “developing a plan to require our customers to implement advanced security controls, like multi-factor authentication (MFA) or network policies, especially for